Web of Trust
A web of trust is a decentralized model for establishing the authenticity of digital identities, in which individuals vouch for one another rather than relying on a central certificate authority. OMXUS implements a physical web of trust through in-person NFC ring activation and vouching, combining the cryptographic rigor of PGP with the social accountability of face-to-face verification.
History
Phil Zimmermann and PGP
The web of trust concept was introduced by Phil Zimmermann in 1992 as part of Pretty Good Privacy (PGP), an email encryption program that Zimmermann released as freeware in response to proposed U.S. legislation (Senate Bill 266) that would have required backdoors in all encryption products.[1] Zimmermann faced a three-year federal investigation for allegedly violating arms export regulations, since strong cryptography was classified as a munition under U.S. law. The case was dropped in 1996, but it galvanized the cypherpunk movement and established the principle that ordinary citizens have a right to strong encryption.
In PGP, users generate cryptographic key pairs and sign each other's public keys to indicate they have verified the key owner's identity. Trust propagates transitively: if Alice trusts Bob, and Bob has signed Carol's key, Alice can assign some confidence to Carol's identity. This model was revolutionary because it eliminated the need for a centralized authority to broker trust between strangers.
Key-Signing Parties
PGP key-signing parties became a social ritual in the cryptography and free software communities during the 1990s and 2000s. Participants would meet in person, verify government-issued identification, exchange key fingerprints printed on slips of paper, and sign each other's keys after the event. Major conferences like DEFCON, FOSDEM, and Chaos Communication Congress hosted large-scale signing events, sometimes with hundreds of participants. The Zimmermann-Sassaman key-signing protocol, developed to scale these events, introduced structured rounds where participants lined up in two facing rows and verified each person systematically.
These parties served a dual purpose: they strengthened the cryptographic trust graph, and they reinforced the social norm that identity verification is a communal responsibility rather than a bureaucratic one.
OpenPGP and GPG
The PGP protocol was standardized as OpenPGP (RFC 4880) by the IETF, and the GNU Privacy Guard (GPG) provided a free software implementation. GPG remains widely used for signing software packages, encrypting email, and verifying commits in version control systems. The key servers that distributed public keys — such as the SKS keyserver network — became the infrastructure of the original web of trust, though they faced persistent problems with spam, certificate flooding attacks, and the inability to delete compromised keys.
Contrast with PKI
The dominant alternative to web of trust is Public Key Infrastructure (PKI), a hierarchical model where trusted Certificate Authorities (CAs) issue digital certificates. PKI underlies HTTPS, corporate networks, and most internet security. The CA model consolidated rapidly: by 2023, just three certificate authorities (Let's Encrypt, DigiCert, and Sectigo) issued the vast majority of TLS certificates on the public internet.[2]
| Property | Web of Trust | PKI (Certificate Authorities) |
|---|---|---|
| Trust source | Peer-to-peer vouching | Centralized authority |
| Single point of failure | None | CA compromise affects all certificates |
| Cost | Free | Certificates historically cost money (now often free via Let's Encrypt) |
| Revocation | Distributed, slow | Centralized, fast (CRL/OCSP) |
| Scalability | Limited by social connections | Scales via hierarchy |
| Identity verification | Variable (depends on participants) | Standardized (depends on CA policy) |
| Censorship resistance | High — no authority can revoke | Low — CAs can revoke under government pressure |
| Privacy | Social graph exposed on keyservers | Certificate transparency logs are public |
| Key recovery | No central recovery mechanism | CA can reissue certificates |
The CA model has suffered notable failures. In 2011, the Dutch CA DigiNotar was compromised by Iranian state actors, who issued fraudulent certificates for Google, Yahoo, and Mozilla domains to intercept dissidents' communications. The CA was revoked and the company went bankrupt. In 2015, the Chinese CA CNNIC issued unauthorized certificates, leading Google and Mozilla to distrust it. These incidents demonstrated the fundamental weakness of hierarchical trust: the entire system is only as strong as its weakest trusted authority.
How It Works
Trust Signatures
When user A vouches for user B:
- A verifies B's identity (ideally in person)
- A cryptographically signs B's public key
- This signature is published, asserting: "A believes this key belongs to B"
The signature includes metadata: the date of signing, the level of trust assigned, and optionally the method of verification used (in-person document check, video call, long-standing personal relationship, etc.).
Transitive Trust
Trust can flow through chains:
- Direct trust — A has personally verified B
- Indirect trust — A trusts B, and B has verified C, so A assigns partial trust to C
- Trust depth — Most implementations limit chain length (typically 2-3 hops) to prevent trust dilution
- Trust breadth — Some models require multiple independent paths to establish confidence (e.g., three marginally trusted signatures equal one fully trusted)
Trust Levels
PGP defined several trust levels:
- Unknown — No information about the key owner's reliability as a verifier
- Untrusted — Explicitly not trusted to verify others
- Marginal — Somewhat trusted (multiple marginal signatures may equal full trust)
- Full — Completely trusted to verify others
- Ultimate — Reserved for the user's own keys
Graph Theory and Trust Networks
Web of trust networks can be analyzed using graph theory. The strongly connected set is the largest subset of keys where every key can reach every other key through trust signatures. Research by Ulrich, Enge, and others showed that the PGP web of trust had a giant strongly connected component containing roughly 50,000 keys by 2009, with an average path length of about 6 hops — consistent with small-world network properties.[3]
Key metrics for web of trust health include:
- Mean shortest distance (MSD) — Average number of hops between any two keys
- Reachability — Percentage of keys reachable from any given key
- Clustering coefficient — Degree to which keys form local clusters
- Betweenness centrality — Identification of keys that serve as critical bridges
Weaknesses of Traditional Web of Trust
- Key management burden — Users must generate, backup, and protect private keys; attend signing events; and maintain revocation lists. The cognitive overhead excluded non-technical users almost entirely.
- Metadata exposure — The public signature graph on keyservers reveals social connections. Intelligence agencies can map activist networks, journalist sources, and organizational structures from the public trust graph alone.
- Cold start problem — New users have no trust connections and cannot immediately participate, creating a chicken-and-egg barrier to adoption.
- Uneven participation — Power-law distribution means a few well-connected individuals (such as Debian developers or FSF board members) become de facto authorities, partially recreating the centralization that web of trust was designed to avoid.
- Certificate flooding — Attackers could upload thousands of fake signatures to a key on public keyservers, making the key unusable. This attack was demonstrated against several prominent GPG keys in 2019.
- No key recovery — Losing a private key means losing the identity entirely, with no mechanism to recover or transfer the accumulated trust.
Modern Alternatives and Evolution
TOFU (Trust on First Use)
Signal, SSH, and other systems use a simplified model where the first key presented is trusted, and changes trigger warnings. This eliminates the verification ceremony but provides weaker guarantees.
Keybase
Keybase (acquired by Zoom in 2020) linked cryptographic keys to social media identities, creating a proof chain: "This Twitter account, this GitHub account, and this PGP key all belong to the same person." This reduced the cold start problem but introduced dependency on corporate platforms.
Decentralized Identifiers (DIDs)
The W3C Decentralized Identifiers standard provides a framework for self-sovereign identity that learns from web of trust's failures: keys are rotatable, verification methods are pluggable, and the social graph can be kept private.[4]
OMXUS Implementation
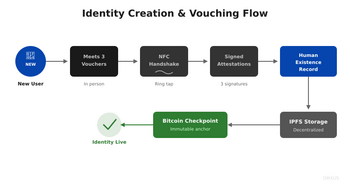
OMXUS addresses the weaknesses of the traditional web of trust by implementing a physical web of trust that combines cryptographic verification with embodied social accountability.
In-Person Vouching
Identity creation requires physical proximity:
- An existing member meets the new user in person
- Both tap their NFC rings together
- The voucher attests to the new user's identity
- This attestation is cryptographically signed and anchored to the Bitcoin blockchain
The physical requirement means that vouching is a deliberate social act, not a casual digital click. The voucher is looking the new member in the eye, staking their reputation on a person they can see and hear.
Sybil Resistance
The physical requirement makes Sybil attacks extremely expensive. Creating fake identities requires recruiting real humans willing to vouch in person, unlike purely digital systems where one person can create thousands of accounts. The cost of a Sybil attack scales linearly with the number of fake identities desired, and each fake identity requires corrupting a real person — a fundamentally different threat model than automated account creation.
Privacy-Preserving Graph
Unlike PGP keyservers, OMXUS uses zero-knowledge proofs to verify trust relationships without exposing the full social graph. A verifier can confirm "this person is vouched for" without learning by whom. This eliminates the metadata exposure problem that made the PGP web of trust a surveillance liability.
Accountability and Reputation
Vouchers bear responsibility for those they introduce to the network. If a vouched identity is found to be fraudulent, the voucher's reputation is affected through a graduated accountability mechanism:
- First fraudulent vouch: warning and reputation reduction
- Repeated fraudulent vouching: temporary suspension of vouching privileges
- Systematic abuse: network review and potential exclusion
This creates skin in the game: vouching is not costless, and vouchers are incentivized to verify carefully.
Key Recovery
Unlike PGP, OMXUS supports social key recovery. If a member loses their ring, a threshold of their vouchers can attest to their identity and authorize a new ring, eliminating the catastrophic key loss problem.
Comparison of Trust Models
| Feature | PGP Web of Trust | PKI/CA | Worldcoin | OMXUS Web of Trust |
|---|---|---|---|---|
| Verification method | Document check at signing party | CA validates domain/org | Iris biometric scan | In-person NFC ring tap |
| Privacy | Poor (public keyservers) | Moderate (CT logs) | Poor (biometric database) | Strong (zero-knowledge proofs) |
| Sybil resistance | Low | Moderate | High | High |
| Cold start | Difficult | Easy (pay CA) | Easy (scan iris) | Moderate (find a member) |
| Decentralization | High | Low | Low (Worldcoin Foundation) | High |
| Key recovery | None | CA reissue | Biometric re-scan | Social recovery via vouchers |
| Accountability | None | Legal liability of CA | None | Voucher reputation at stake |
See Also
- Decentralized Identifiers
- Sybil Resistance
- NFC Technology
- Human Verification API
- Getting Started
- Privacy Architecture
- RGB Protocol
- Main Page
References
[5] [6] [7] [8] [9] [10] [11] [12] [13]
- ↑ Zimmermann, P. (1995). The Official PGP User's Guide. MIT Press.
- ↑ W3Techs. (2023). "Usage of SSL certificate authorities for websites."
- ↑ Ulrich, A. (2011). "Investigating the OpenPGP Web of Trust." European Conference on Information Warfare and Security.
- ↑ W3C. (2022). Decentralized Identifiers (DIDs) v1.0. W3C Recommendation.
- ↑ Zimmermann, P. (1995). The Official PGP User's Guide. MIT Press.
- ↑ Abdul-Rahman, A., & Hailes, S. (2000). "Supporting Trust in Virtual Communities." Proceedings of the 33rd Hawaii International Conference on System Sciences.
- ↑ Caronni, G. (2000). "Walking the Web of Trust." Proceedings of the 9th IEEE International Workshops on Enabling Technologies.
- ↑ W3C. (2022). Decentralized Identifiers (DIDs) v1.0. W3C Recommendation.
- ↑ Ulrich, A. (2011). "Investigating the OpenPGP Web of Trust." European Conference on Information Warfare and Security.
- ↑ W3Techs. (2023). "Usage of SSL certificate authorities for websites."
- ↑ Zimmermann, P. (1991). "Why I Wrote PGP." Essay distributed with PGP source code.
- ↑ Penning, H. P. (2006-2019). "Analysis of the Strong Set in the PGP Web of Trust." https://pgp.cs.uu.nl/.
- ↑ Levien, R. (2009). "Attack Resistant Trust Metrics." Computing with Social Trust, Springer.