NFC Technology
Near-field communication (NFC) is a set of short-range wireless communication protocols operating at 13.56 MHz, enabling data exchange between devices within approximately 4 centimeters. OMXUS uses NFC rings as the physical layer for identity verification, vouching, and voting.
How NFC Works
Physical Principles
NFC operates via electromagnetic induction between two loop antennas. When an NFC reader generates a radio frequency field, a nearby NFC tag or device can:
- Passive mode — Draw power from the reader's field and respond (no battery required)
- Active mode — Both devices generate their own fields and alternate transmission
The extremely short range (typically under 4 cm) is a security feature, not a limitation. It ensures that communication requires deliberate physical proximity.
ISO Standards
NFC is governed by several international standards:
| Standard | Purpose |
|---|---|
| ISO/IEC 14443 | Proximity cards (Type A and B) |
| ISO/IEC 18092 | NFC interface and protocol (NFCIP-1) |
| ISO/IEC 15693 | Vicinity cards (longer range, lower data rate) |
| ISO/IEC 21481 | NFC interface and protocol (NFCIP-2) |
Operating Modes
- Reader/Writer — NFC device reads or writes to a passive tag
- Peer-to-Peer — Two active NFC devices exchange data bidirectionally
- Card Emulation — NFC device behaves as a contactless smart card
Security Properties
NFC's security characteristics make it suitable for identity applications:
Inherent Properties
- Proximity requirement — The 4 cm range makes remote interception extremely difficult
- Physical presence — Communication implies the devices are nearly touching
- Bidirectional authentication — Both parties can verify each other
Cryptographic Capabilities
Modern NFC chips support:
- AES-128 and AES-256 encryption
- Elliptic curve cryptography (ECC)
- Secure element storage for private keys
- Hardware random number generation
- Tamper detection and response
Attack Vectors
| Attack | Feasibility | Mitigation |
|---|---|---|
| Eavesdropping | Very difficult (requires <1m proximity) | Encryption on secure channel |
| Relay attack | Possible but requires real-time relay | Time-bounding protocols, challenge-response |
| Data modification | Detectable | Cryptographic integrity checks |
| Cloning | Prevented by secure element | Private keys never leave the chip |
Common Use Cases
- Contactless payment — Apple Pay, Google Pay, bank cards
- Access control — Building entry, hotel room keys
- Transit — Oyster Card, Suica, transit passes worldwide
- Identity — ePassports, national ID cards (used in 150+ countries)
- Data sharing — Contact exchange, Wi-Fi pairing, Bluetooth bootstrapping
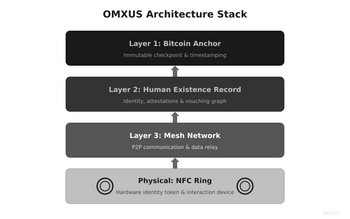
The OMXUS NFC Ring
OMXUS chose an NFC ring as its identity device for specific reasons:
Why a Ring?
- Always worn — Unlike a card or phone, a ring is a natural accessory
- No battery — Passive NFC draws power from the reader device
- Discreet — Does not advertise itself as a technology device
- Cultural universality — Rings are worn across all cultures
- Durability — No moving parts, no screen to crack, waterproof
Technical Specifications
- Chip: Secure element with ECC key storage
- Frequency: 13.56 MHz (ISO 14443-A)
- Range: 1-4 cm (requires deliberate tap)
- Storage: Decentralized identifier (DID), cryptographic keys
- Material: Ceramic or titanium housing
- Power: Passive (harvests energy from reader field)
- Lifespan: No battery; functionally unlimited
Operations
The ring performs several functions within the OMXUS system:
- Identity assertion — Tap to prove you are a verified human
- Vouching — Tap rings together to vouch for a new member
- Voting — Tap to sign and cast a vote
- Emergency response — Tap to witness or respond to an emergency
Why Not Biometrics?
OMXUS deliberately chose NFC over biometric identification:
- Revocability — A compromised ring can be replaced; a compromised fingerprint cannot
- Consent — A ring tap is a deliberate action; facial recognition can operate without consent
- Privacy — A ring stores a cryptographic key, not biological data
- Coercion resistance — A ring can be left at home; a face cannot
See Also
References
- ISO/IEC 14443:2018. Identification cards — Contactless integrated circuit cards — Proximity cards.
- ISO/IEC 18092:2013. Information technology — Telecommunications and information exchange between systems — Near Field Communication.
- Coskun, V., Ozdenizci, B., & Ok, K. (2013). "A Survey on Near Field Communication Technology." Wireless Personal Communications, 71(3), 2259-2294.
- Haselsteiner, E., & Breitfuss, K. (2006). "Security in Near Field Communication." Workshop on RFID Security.