Technical Architecture
Jump to navigation
Jump to search
The OMXUS Technical Architecture is a four-layer system designed for 30 million users, resilience against any single point of failure, and independence from centralized infrastructure.
Layer Overview
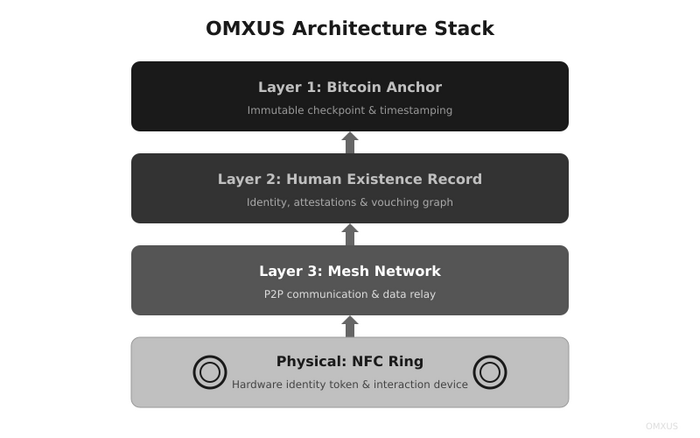
+---------------------------------------------------------------------+
| LAYER 1: BITCOIN ANCHOR |
| Permanent. Immutable. "This happened." |
+---------------------------------------------------------------------+
^
+---------------------------------------------------------------------+
| LAYER 2: HUMAN EXISTENCE RECORD |
| Identity. One per human. Stored on IPFS. |
+---------------------------------------------------------------------+
^
+---------------------------------------------------------------------+
| LAYER 3: MESH NETWORK |
| Yggdrasil + QUIC + LoRa. Works offline. |
+---------------------------------------------------------------------+
^
+---------------------------------------------------------------------+
| PHYSICAL: NFC RING |
| $9. No battery. Tap to do everything. |
+---------------------------------------------------------------------+
Layer 1: Bitcoin Anchor
Purpose
Permanent, immutable record of critical events. "This happened."
Implementation
- RGB Protocol — Smart contracts on Bitcoin's UTXO model
- Periodic checkpoints — Aggregated records anchored to blockchain
- Merkle trees — Efficient verification of any record
- No separate blockchain — Uses Bitcoin's security
What's Anchored
- Identity attestations (vouching records)
- Vote tallies (not individual votes)
- Epoch boundaries
- Major governance decisions
Layer 2: Human Existence Record (HER)
Purpose
One identity per human. Sybil-resistant. Self-sovereign.
Implementation
- DID (Decentralized Identifier) — W3C standard
- IPFS storage — Content-addressed, distributed
- Three-voucher attestation — In-person verification
- Proof Capsule — Personal backup of identity proof
Structure
Each HER contains:
- DID and public key
- Voucher signatures (3 required)
- Timestamp of creation
- Hash links to checkpoint chain
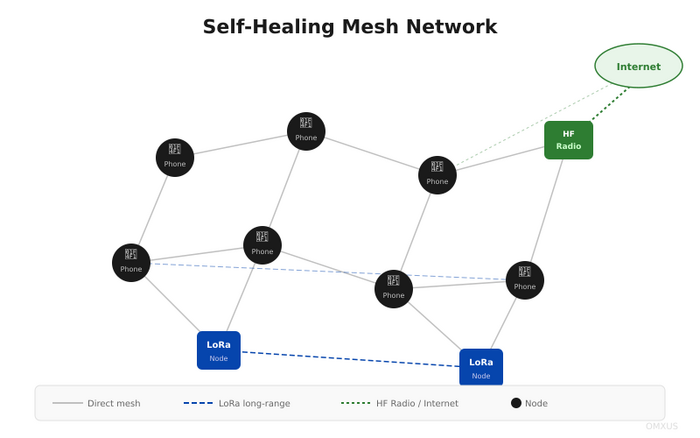
Layer 3: Mesh Network
Purpose
Communication independent of centralized infrastructure.
<iframe width="560" height="315" src="https://www.youtube.com/embed/dE1DuBesGYM" frameborder="0" allowfullscreen></iframe>
Primary: Yggdrasil
- Encrypted IPv6 mesh overlay
- Cryptographic addressing
- Routes through any available path
- Self-healing around failures
Transport: QUIC
- Modern transport protocol
- Low latency
- Connection migration
- Multiplexed streams
Fallback: LoRa
- Long-range radio (kilometers)
- Low bandwidth, high reliability
- Works without infrastructure
- Battery-efficient
Emergency: HF Radio
- Global communication without any infrastructure
- Last resort fallback
- Community-operated stations
Offline: Sneakernet
- Physical transport of data
- Works when all else fails
- QR codes, USB drives, printed books
Physical Layer: NFC Ring
Purpose
Physical anchor of identity. Tap to act.
Specifications
- Interface: ISO 14443-A/B NFC at 13.56 MHz
- Secure element: EAL5+ certification
- Storage: Primary DID key pair + recovery shards
- Water resistance: IPX8
- Materials: Medical-grade titanium or ceramic
- Power: None (inductively powered during NFC)
- Cost: $9 at scale
Functions
- Sign votes
- Activate emergencies
- Verify identity
- Vouch for others
- Complete contracts
Data Flow
Voting
- User sees proposal in app
- User makes choice
- Ring signs vote
- Vote propagates via mesh
- Aggregated to regional tallies
- Tallies anchored to Bitcoin
Emergency
- User taps ring (emergency pattern)
- Alert broadcasts via mesh
- Nearby devices receive immediately
- Responders acknowledge
- Location shared (only during emergency)
- Response logged
Identity Creation
- New user meets 3 vouchers
- Each voucher signs attestation
- Attestations bundled
- HER created on IPFS
- Eventually checkpointed to Bitcoin
Scale Architecture (30M Users)
Geographic Hierarchy
Australia (30M)
|
+-- States (8)
|
+-- Regions (~100)
|
+-- Districts (~1,000)
|
+-- Neighborhoods (~10,000)
|
+-- Blocks (~100,000)
Vote Aggregation
- Block votes aggregate to neighborhood
- Neighborhood to district
- District to region
- Region to state
- State to national
- Each level signs the aggregation
Load Distribution
- No central server
- Each node handles local traffic
- Aggregation happens at edges
- Only tallies propagate up
Security Model
No Central Point of Failure
- No master server
- No admin accounts
- No kill switch
- No central database
Cryptographic Guarantees
- Ed25519 signatures (ring)
- BLS aggregation (votes)
- AES-256 encryption (data)
- SHA-256 hashing (integrity)
Defense in Depth
- Multiple network paths
- Multiple storage locations
- Multiple verification methods
- Multiple fallback systems
Privacy Model
What's Public
- Vouching chains
- Vote tallies (not individual votes)
- Contract completions
- Reputation scores
What's Private
- Individual votes (encrypted, revealed only in aggregate)
- Location (except during emergencies)
- Personal data (encrypted, user-controlled)
- Communication content